Unified DFIR Ecosystem
Native, portable tools without dependencies for triage, analysis, and correlation.

Native, portable tools without dependencies for triage, analysis, and correlation.

A comprehensive forensic environment, composed of lightweight, portable tools designed for live or post-mortem analysis.
Advanced PowerShell script for Windows triage. Collects forensic artifacts (Prefetch, Amcache, SRUM, USB, Events, Shimcache, etc.). Compatible with direct execution on compromised machines or via EDR/XDR consoles.
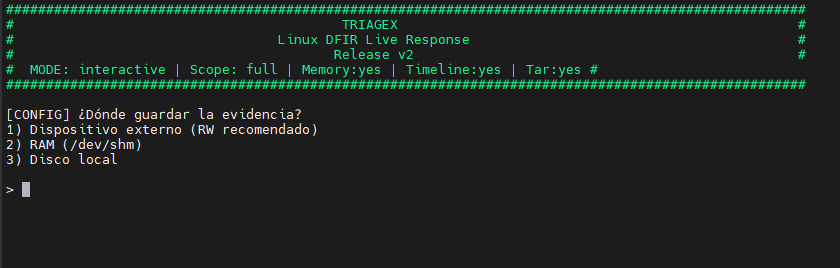
Standalone Bash tool for rapid Linux analysis. Extracts logs, sessions, active connections, scheduled tasks, users, cronjobs, recent commands, and persistence artifacts.
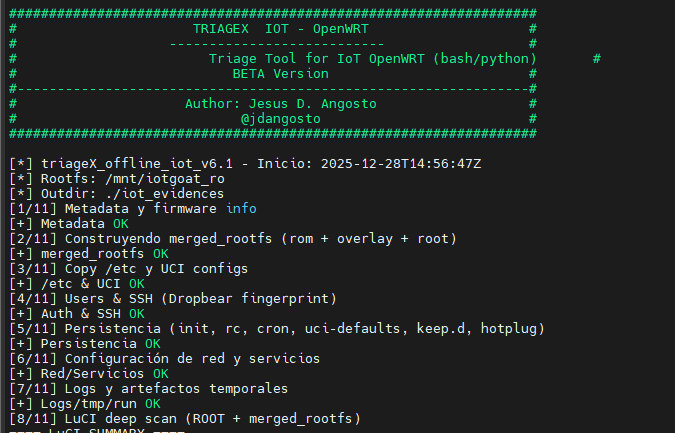
Specialized version for IoT and embedded environments. Integrates Python modules to analyze configurations, authentications, credentials, critical services, and vulnerabilities.
Unified platform that centralizes triage results, generates interactive timelines (Chronos) and relationship graphs (Nexus), with automatic MITRE labeling and reporting.
Normalization engine that converts raw evidence into structured data. Multi-cloud support (AWS, Azure, M365, GCP) and log processing for Chronos and Nexus.
Interactive timeline generation to visualize events in chronological order and detect attack patterns.
Graph analysis to visualize complex relationships between artifacts, users, and affected systems.
The analysis layer that unifies Chronos — Timeline and Nexus — Graph, designed for DFIR teams that need to move from isolated artifacts to complete investigations.
The platform centralizes triage results, enables case management, evidence tagging, and the construction of timelines and relationship graphs ready to present in reports and technical committees.
It is oriented towards Enterprise environments where repeatable workflows, change control, and collaboration between analysts are required.
PowerForensics Platform is our proprietary technology. We do not sell the software; we use it to offer you the fastest and deepest incident response service on the market.
PowerTriage is a native PowerShell tool designed for Windows (10/11/Server) capable of collecting and analyzing key system artifacts. It works without external dependencies and can be executed directly from an EDR/XDR environment or remote Live Response.
Incident Response Teams, Corporate DFIR, SOC, Hybrid or Air-gapped environments.
Standalone Bash tool for rapid analysis on Linux systems. Extracts logs, sessions, active connections, tasks, users, cronjobs, and persistence artifacts.
Specialized version for embedded environments. Analyzes configurations, credentials, critical services, and vulnerabilities.
I am open to collaborations, feedback on the platform, or simply chatting about DFIR. If you are interested in the project or want to report an issue, write to me.